We are still actively working on the spam issue.
Anonymizing yourself
The internet is a cruel and horrible place. You might want to drop out of the matrix and join an anonymous network. A broad approach on how to start evading global data surveillance and improving your overall online privacy can be found here.
Contents
Anonymous Networks
Tor
Main article: Tor
Let's get something clear: Tor is NOT illegal to use (unless you live in one of those crazy whackjob countries run by a militant dictator). Tor traffic was NOT significantly reduced by the removal of Silk Road, and as far as is known, new compromises for the underlying Tor framework did not come about from the removal of Silk Road. If you are interested, concerned or sceptical, check out this video here and read the FAQ.
Tor sets up a SOCKS proxy to the normal internet, allowing you to send any application’s connection anonymously through the Tor network. Any connections made through Tor will be anonymised but not confidential unless you use end to end encryption in the application, like SSL/TLS for web browsing, or an SSH tunnel. Torrenting is discouraged as it uses up too much bandwidth.
I2P
I2P is end to end encrypted and separate from the normal internet; this means that connections through I2P are confidential and anonymous. No-one can know who you are talking to, or what you are saying to them, because there are no exit nodes. Tor hidden services (.onions) work in a similar way. All internet applications can be forwarded through I2P including ed2k, Gnutella, and torrents. Torrenting is encouraged on the I2P network, although you cannot connect to non-I2P torrent swarms. Internal services that would be called onions on the TOR network are called eepsites on the I2P network
Freenet
Freenet is a distributed filesystem, where you can store files ‘in the cloud’ and download them anonymously from the Freenet network. Many of the files are HTML pages which can be viewed as static websites using a browser, and many are standalone files which can be searched and downloaded anonymously. Freenet content is undeletable as there is no way of knowing which node is holding each file.
Please note that its also chock-full of CP.
Browsers
Safe Practices
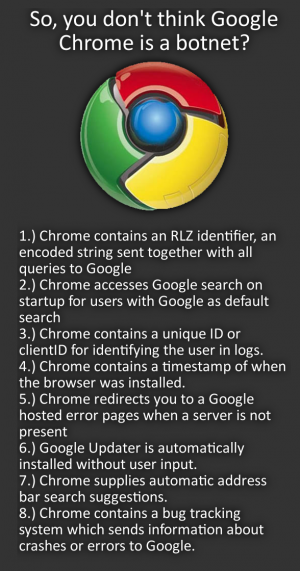
- Always use an open-source browser. This ensures it can be freely audited. Remember: Google Chrome is not open-source, Chromium is.
- Use a search engine that respects your privacy such as DuckDuckGo or StartPage instead of Google or Bing.
Chromium
Using Chromium is generally unrecommended because even though you can disable it's known tracking features (the RLZ identifier is in Chrome, not Chromium), Chromium's code isn't as audited as Firefox's and Chromiums security addons aren't up to par with Firefox's yet. If you absolutely refuse to use anything else, follow these instructions:
- If you seriously sync Chromium to your Google account, you are a fucking dumbass. De-sync the two immediately.
- Go to your settings menu, click advanced settings scroll down to privacy, and turn everything off.
- Go to Content Settings above that and check "Block 3rd party cookies and site data"
- Unless you want to use a script blocker, also turn off Javascript.
- Now scroll down to "Continue running background apps while Chromium is closed" and disable that as well unless you trust your addons.
Setting Startpage As A Search Engine
What is given to you by Startpage's website wont work, so use this link in the third box when adding it as a search engine: https://startpage.com/do/search?query=%s&cat=web&pl=chrome&language=english
Security Extensions
See them here.
Mozilla Firefox
To ensure maximum security while browsing the internet, always turn off third party cookies. Mozilla describes them as: For example, cnn.com might have a Facebook like button on their site. That like button will set a cookie that can be read by Facebook. That would be considered a third-party cookie.
Change your search engine. There are ways to get around Google’s insane profiling. See Search engines.
Security Extensions
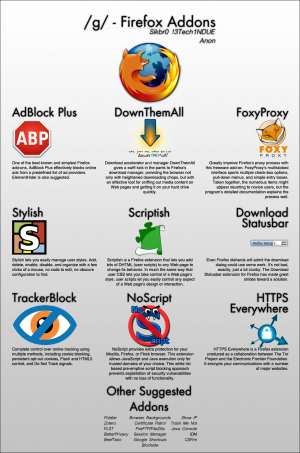
There are many extensions available for Firefox to make you less trackable. Read the Firefox article for a comprehensive list of addons.
Fingerprinting
Fingerprinting is the process of using otherwise non-identifying information to identify you. When enough non-identifying information is collected, you will usually be unique amongst others.
| Threat | Countermeasure |
|
Recommended: Disable and uninstall browser Plugins (note: Plugins are different than Extensions) such as Flash and Java.
Alternative: Set the plugin to "Ask to activate". You will still be vulnerable whenever you activate that plugin. |
|
Recommended: Disable Javascript
Alternative: Use NoScript to whitelist Javascript on a site-by-site basis. You will still be vulnerable on those sites. |
|
Recommended: Use an extension such as Secret Agent to randomize header information. |
|
Disable 3rd Party Cookies and use an extension such as Self-Destructing Cookies to automatically purge cookies. |
|
Recommended: Use an anonymous network, a non-logging VPN service, or a non-logging proxy service. |
|
Recommended: Use an extension such as Request Policy to selectively whitelist such requests. |
|
Recommended: Turn off sending HTTP referer information.
Alternative: Install an extension such as Smart Referer to keep referer information limited to a single domain. |
See also: EFF Panopticlick and evercookie.
DNS
DNS is what allows your computer to convert a domain name (such as wiki.installgentoo.com) into an IP address to connect to. That process is called resolving. When your computer attempts to resolve a domain name it queries a DNS server. Usually this will belong to your ISP if you have not configured it manually. Not all DNS servers are created equal. Some block queries to certain websites, some hijack queries and redirect them elsewhere, and some log your queries. You should look for a DNS server that is close by (to reduce latency in your requests) that doesn't log your IP address. In addition, you may want to use DNSCrypt for added protection.
Warning: Google DNS and OpenDNS log queries. Google "anonymizes" query information after a period of time, but keeps associated ISP information permanently.[1] OpenDNS logs your IP address and may also correlate it with other information that is normally non-personally identifying.[2] Avoid those two services.
DNSCrypt
End-to-end encryption for your DNS requests. This prevents any intermediaries from monitoring your DNS requests. It defaults to OpenDNS. You should change that using one of the additional DNS servers listed on dnscrypt.org.
See DNSCrypt for more information.
OpenNIC
The OpenNIC Project is a privacy-minded collection of volunteer-run servers that also allow you to use extra TLDs such as .geek etc. Also features DNSCrypt support.
Operating Systems
While unfortunately, government organizations around the world have a variety of backdoors into a variety of operating systems, one can still attempt to be anonymous through a variety of methods. Free software alternatives to Windows or Mac OS appear to be more secure than their counterparts, since their code is almost always individually reviewed.
Tails
Tails is an OS specifically created to aim at preserving your privacy and anonymity. It forward all your packets through TOR network and leave no trace on the computer you are using it on. Your files and emails are also encrypted using top of the line cryptographic tools.
Android
By their nature cellphones cannot be completely anonymous, but there are some steps that can be taken to at least limit your footprint.
Android Replacements
- Replicant: A project to completely replace all proprietary components of Android.
- Custom ROMs
- Firefox OS: An alternative operating system by Mozilla that runs on some Android devices.
Alternative Google Apps
- F-Droid: Part of the Replicant project. An app store that only contains Free Open Source Software.
- NOGAPPS Project: Replaces the Play Store, Google Maps API, Network Location API, and others in the future.
- APK Downloader
- OsmAnd~: Replacement for Google Maps.
- GApps Browser
Removing Ads
- AdAway: Hosts file based ad-blocking. (Requires root)
- Adblock Plus
- Lucky Patcher: Patches APKs to remove ads and allows you to disable the ad's activity itself. (Requires root)
Enforcing Permissions
- XPrivacy
- App Ops: Available since Android 4.3. Removed in 4.4.2, but still retained in custom ROMs. Allows you to tweak individual permissions on a per-app basis.
Browsers
Related Links
- http://browserspy.dk/
- http://www.areweprivateyet.com/
- https://www.howsmyssl.com/
- https://www.dnsleaktest.com
- http://www.whatismyreferer.com/
- https://panopticlick.eff.org/
- https://securityinabox.org/en
- https://myshadow.org/
- https://ssd.eff.org/
- http://login2.me/
- http://bugmenot.com/
OPSEC/Operational Security
All the software in the world won't help you if ignore the human element. Obvious no-nos:
- Using the same username everywhere.
- Using the same email address everywhere.
- Logging into the same accounts through your real ip and a proxy/vpn/tor.
- Posting photos or images which can be traced back to you via a reverse image search.
Dread Pirate Roberts was brought down by many of the above points.
More subtle no-nos:
- Forensic Linguistics is the science of figuring out someone's identity by the words, phrases and grammar they use.
- Using the same browser with your real ip as your proxy/vpn/tor ip (see fingerprinting above).
- Discussing personal preferences, or knowledge of specific locations such as a school, shop or town.
- Being unprepared for a proxy/vpn/tor to drop out.
Steve Rambam gave an excellent talk at the HOPE hacker conference which summarizes many of the techniques that you/private investigators/lea can use to determine someone's identity.
To err is human. As clever as you think you are, all it takes is one connection from your real ip address to deanonymize you. One day when you're distracted/tried/stressed/drunk/high/panicked/surprised or when something out of the ordinary is happening, you will mess up. Putting up many automated layers of anonymity/security will help protect you from yourself.