We are still actively working on the spam issue.
Difference between revisions of "Setting up a Server"
Toynbeeidea (talk | contribs) |
|||
| Line 1: | Line 1: | ||
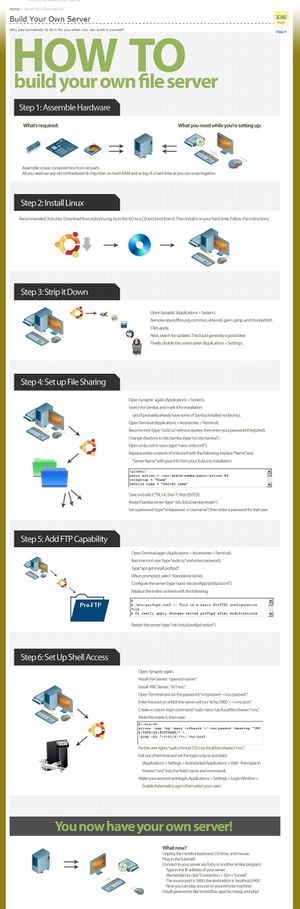
[[File:Setting_up_a_Fileserver.jpeg|thumb|The gist of things]] | [[File:Setting_up_a_Fileserver.jpeg|thumb|The gist of things]] | ||
| − | Need to [http://wiki.installgentoo.com/index.php?title=Email#Self_Hosted_Email selfhost] mail? Need a fileserver? Well, here's some advice. | + | Need to [http://wiki.installgentoo.com/index.php?title=Email#Self_Hosted_Email selfhost] mail? Need a fileserver? Well, here's some advice. We're gonna try to write this like you've never done this shit before. It does, however, assume you have at least some basic [[GNU/Linux]] knowledge. If you don't, you probably aren't ready for this - just stick with FreeNAS or NAS4Free. |
| + | |||
| + | A lot of this applies to both a physical machine as well as a [[VPS]] setup. | ||
== Protecting Your Private Network == | == Protecting Your Private Network == | ||
| Line 7: | Line 9: | ||
== Protecting from DDoS and shit == | == Protecting from DDoS and shit == | ||
Use [http://www.fail2ban.org/wiki/index.php/Main_Page Fail2Ban] and perhaps a redundant computer in the DMZ. Also never use passwords, only keyfiles. | Use [http://www.fail2ban.org/wiki/index.php/Main_Page Fail2Ban] and perhaps a redundant computer in the DMZ. Also never use passwords, only keyfiles. | ||
| + | |||
| + | == Securing your shell == | ||
| + | |||
| + | Add a non-root user. Then, while logged in as root, do this: | ||
| + | |||
| + | visudo | ||
| + | |||
| + | Go down to the bit where it says ''# User privilege specification'', and copy the setup for the root line. So, if your non-root user is "faggot," it will look like so: | ||
| + | |||
| + | # User privilege specification | ||
| + | root ALL=(ALL) ALL | ||
| + | faggot ALL=(ALL) ALL | ||
| + | |||
| + | Install [http://www.chiark.greenend.org.uk/~sgtatham/putty/download.html PuTTY], on a different machine than the one you are setting up as the server. This will include PuTTYGen. | ||
| + | |||
| + | Run PuTTYGen to generate a public/private key pair. Go with SSH-2 DSA, 4096 bits - nobody's gonna crack that shit easily. When done, it will display your public key. Copy and paste that text into a text file, but omit the last bit that says "dsa-key-########". DO NOT PUT IN A PASSPHRASE. Save the private key. | ||
| + | |||
| + | Open PuTTY and log in as your non-root user. Then do this: | ||
| + | |||
| + | mkdir /home/faggot/.ssh | ||
| + | nano /home/faggot/.ssh/authorized_keys | ||
| + | |||
| + | Paste your public key that you saved as a text file and paste it in. MAKE SURE IT IS ALL ONE LINE, like so: | ||
| + | |||
| + | ssh-dsa [insanely long string of crap] | ||
| + | |||
| + | And save it. | ||
| + | |||
| + | Now take ownership of it: | ||
| + | |||
| + | chmod 600 ~/.ssh/authorized keys | ||
| + | |||
| + | DO NOT LOG OUT OF PuTTY, but open another connection to your server, only this time point PuTTY to your private key file to test it out. If it all goes well, your login will look something like this: | ||
| + | |||
| + | Using username "faggot". | ||
| + | Authenticating with public key "dsa-key-########" | ||
| + | |||
| + | Assuming that works, close your previous PuTTY session and do this: | ||
| + | |||
| + | |||
[[Category:Tutorials]] | [[Category:Tutorials]] | ||
Revision as of 17:11, 4 February 2014
Need to selfhost mail? Need a fileserver? Well, here's some advice. We're gonna try to write this like you've never done this shit before. It does, however, assume you have at least some basic GNU/Linux knowledge. If you don't, you probably aren't ready for this - just stick with FreeNAS or NAS4Free.
A lot of this applies to both a physical machine as well as a VPS setup.
Protecting Your Private Network
Use a DMZ, nigger.
Protecting from DDoS and shit
Use Fail2Ban and perhaps a redundant computer in the DMZ. Also never use passwords, only keyfiles.
Securing your shell
Add a non-root user. Then, while logged in as root, do this:
visudo
Go down to the bit where it says # User privilege specification, and copy the setup for the root line. So, if your non-root user is "faggot," it will look like so:
# User privilege specification root ALL=(ALL) ALL faggot ALL=(ALL) ALL
Install PuTTY, on a different machine than the one you are setting up as the server. This will include PuTTYGen.
Run PuTTYGen to generate a public/private key pair. Go with SSH-2 DSA, 4096 bits - nobody's gonna crack that shit easily. When done, it will display your public key. Copy and paste that text into a text file, but omit the last bit that says "dsa-key-########". DO NOT PUT IN A PASSPHRASE. Save the private key.
Open PuTTY and log in as your non-root user. Then do this:
mkdir /home/faggot/.ssh nano /home/faggot/.ssh/authorized_keys
Paste your public key that you saved as a text file and paste it in. MAKE SURE IT IS ALL ONE LINE, like so:
ssh-dsa [insanely long string of crap]
And save it.
Now take ownership of it:
chmod 600 ~/.ssh/authorized keys
DO NOT LOG OUT OF PuTTY, but open another connection to your server, only this time point PuTTY to your private key file to test it out. If it all goes well, your login will look something like this:
Using username "faggot". Authenticating with public key "dsa-key-########"
Assuming that works, close your previous PuTTY session and do this: