We are still actively working on the spam issue.
Cyberpunk
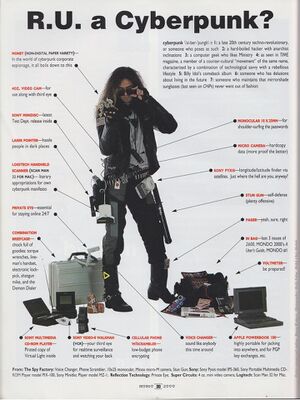
Cyberpunk began as a subgenre of science fiction that's "high tech and low life." The genre generally focuses on the conflict between hackers and corrupt governments and megacorporations, in a dystopian near-future setting. Subtexts of the genre, like in William Gibson's prophetic novel Neuromancer, often deal with the social (and occasionally economic) impacts of new technology like cybernetics.
Originally gaining popularity in the late 20th century, cyberpunk has stood the test of time, as our present-day world starts to move more and more in the direction of the fictional worlds in the aforementioned Neuromancer and Ridley Scott's near-prophetic film Blade Runner.
Soon after its popularity rose, Cyberpunk became a designator for the freelance computer hacker, independent of the literary genre. The author who invented this term was surprised when this occurred. Cyberpunks in this sense are fundamentally a culture of hackers whom use their technological process to augment themselves, and "fite da machine".
On 4chan's /g/, /g/punk threads are up often. 8chan has it's own dedicated board, /cyber/. One of /cyber/'s main contributors, Akitaro Wantanabe, runs a cyberpunk info repo dead.
This page offers the essentials of cyberpunk, what the genre means, and briefly gives guides on how to utilize the cyberpunk lifestyle.
Everyday, we are proving more and more to be in a cyberpunk dystopia.
Contents
[hide]Essential Reading
Lifted from Akitaro's website. (dead link)
William Gibson
The Sprawl Trilogy
- Neuromancer
- Count Zero
- Mona Lisa Overdrive
The Bridge Trilogy
- Virtual Light
- Idoru
- All Tomorrow's Parties
Misc.
- Pattern Recognition
- Zero History
- Burning Chrome
Bruce Sterling
- The Artificial Kid
- Schismatrix
- Islands in the Net
- Heavy Weather
- Holy Fire
- Distraction
- Zeitgeist
Misc.
"To celebrate #/g/sicp's 1.7th birthday (if you count in base 12) we spent the weekend amalgamating all of our collective book libraries, sorting, removing duplicates and trying to get what we believe to be the best collection of tech books we could find for release as a torrent. A magnet link is also available for those who prefer that sort of thing. Alternatively, browse the library and download individual files."
An excellent and thorough introduction to, and overview of, the structure and operation of the Internet.
Things to Know
]
Cryptocurrencies
Main Article: Cryptocurrency
Still swapping dead presidents? My sides are in orbit, chummer. In case you weren't aware, hierarchical trust systems are fundamentally a scam. Maintain your sense of autonomy by using Cryptocurrencies and while you're at learn the ins and outs of cyberpunk:
EFF
Main Article: EFF
The Electronic Frontier Foundation is an international non-profit digital rights group based in the United States. They provide funds for legal defense in court, present friend of the court briefs, defend individuals and new technologies from what it considers baseless or misdirected legal threats, work to expose government malfeasance, provide guidance to the government and courts, organize political action and mass mailings, support some new technologies which it believes preserve personal freedoms, maintain a database and web site of related news and information, monitor and challenge potential legislation that it believes would infringe on personal liberties and fair use, and solicit a list of what it considers patent abuses with intentions to defeat those that it considers without merit.
In short and given the context of cyberspace: they fight for your freedoms.
They also provide tools and information for the privacy-concerned individual, such as:
- Panopticlick - See how unique - and trackable - your browser configuration is.
- HTTPS Everywhere is a browser extension that encrypts your communications with many major websites.
PGP
Main Article: PGP
PGP over time has since been turned into a commodity; open alternatives exist. You can find them here: GnuPG, Open PGP
Pretty Good Privacy (PGP) is a data encryption and decryption computer program that provides cryptographic privacy and authentication for data communication. PGP is often used for signing, encrypting, and decrypting texts, emails, files, directories, and whole disk partitions and to increase the security of e-mail communications. It was created by Phil Zimmermann in 1991 while working at PKWARE, Inc. Nowadays it's primarily used for email.
OTR
Main Article: OTR
Off-the-Record Messaging, commonly referred to as OTR, is a cryptographic protocol that provides strong encryption for instant messaging conversations. OTR uses a combination of the AES symmetric-key algorithm, the Diffie–Hellman key exchange, and the SHA-1 hash function. In addition to authentication and encryption, OTR provides perfect forward secrecy and malleable encryption. The primary motivation behind the protocol was providing deniability for the conversation participants while keeping conversations confidential, like a private conversation in real life, or off the record in journalism sourcing. This is in contrast with other cryptography tools that produce output which can be later used as a verifiable record of the communication event and the identities of the participants. In most cases, people using such cryptography software are not aware of this and might be better served by OTR tools instead. The initial introductory paper was named Off-the-Record Communication, or, Why Not To Use PGP.
With OTR, no one else can read your instant messages.
You are assured the correspondent is who you think it is.
The messages you send do not have digital signatures that are checkable by a third party. Anyone can forge messages after a conversation to make them look like they came from you. However, during a conversation, your correspondent is assured the messages he sees are authentic and unmodified.
And lastly, if you lose control of your private keys, no previous conversation is compromised.
(OTR is slowly being replaced with OMEMO encryption)
Tox
Main Article: Tox
A project that grew out of /g/ after the Snowden Leaks first popped up during the summer of 2013. The project's goal is to create a distributed Skype alternative void of third parties. How they accomplish this is by having users connect directly to their peers.
Tahoe-LAFS
Tahoe-LAFS is a Free and Open cloud storage system. It distributes your data across multiple servers. Even if some of the servers fail or are taken over by an attacker, the entire filesystem continues to function correctly, preserving your privacy and security.
Like ownCloud but less streamlined.
SSL
SSL root certificates, e.g., Verisgn, Comodo, Entrust -- corporations that have placed themselves the top of the pyramid, but why do you trust them? Why should you pay $1500 so a corporate fatcat can vouch for your identity for a year? Self sign your own certificates, anons.
DNS
Main Article: DNS
ICANN has a monopoly on the domain name system, but why? So they can release stupid vanity domains like .donut and .shoes? Top fucking lel. Use ORSN or use a distributed system like Namecoin
For more information on this, see this article.
Circumventing Surveillance in Real Life
Automated systems look for specific points of your bodies and use that information to identify you. Obfuscate these points using the methods suggested and you may reduce your data exhaust.
IRhat
You wouldn't believe how non updated the surveillance infrastructure most cities and their respective businesses have. Many cameras do not have infrared filters on their lenses so all one needs to do is shine infrared light in their direction and all the camera will see is a blur of white light covering where your face should be.
CV Dazzle
Dress like a more fashionable juggalo.
Stealth Wear
Grind up some cheap mylar thermal blankets, make a solution and dip your clothes in it to become invisible to thermal cameras:
Printer Tracking
Your printouts may include hidden information that identifies you. Make sure your printer preserves your anonymity.
CCTV
Avoid surveillance cameras by choosing routes that avoid known locations.
Circumventing Surveillance
For more, see Akitaro's website.
Tor
For a more in depth definition, see The Tor Article and their Official Website.
Tor is free software and an open network that helps you defend against traffic analysis, a form of network surveillance that threatens personal freedom and privacy, confidential business activities and relationships as well as state security. Generally, it is the name of several related and interconnected projects, all centered around providing you with anonymity and privacy online. In the simplest sense, Tor is the name of a free software project that protects your privacy online by bouncing your communications around a distributed network of computers (called "relays") run by volunteers all around the world. This network of relays is called the Tor Network.
- Tor Onion Sites
- Torchan - Started December 2011. Reincarnation of Torchan, the most famous *chan to exist in .onionland. Used to have heavy CP: http://zw3crggtadila2sg.onion/imageboard/
- RundaChan - Started December 2011. New chan. Helpful to newbies: http://vkfwaglwnbi6vl7s.onion/
- Bobby's Board - Started December 2011. New chan. Low uptime: http://uzz3h4ruguwza4fr.onion/imgboard/b/
- Anonchan - Started November 2011. Went viral. Over 1000 posts in first month - http://od6j46sy5zg7aqze.onion/
- Hidden Image Site - Moderated for CP: http://wyxwerboi3awzy23.onion/
- Boards: Mostly SnapBBS. Normal forums
- Networking
- Social networking.
- Torbook - Facebook for Tor. Has a public square for discussions: http://ajqaivfxtqy3fdlr.onion/torbook/
- Questions and Answers - A cool truth game: http://ajqaivfxtqy3fdlr.onion/qa/index.php
- Email/Messaging
- Communication.
- TorPM - Tor private messaging: http://4eiruntyxxbgfv7o.onion/pm/
- Tor Mail - Email services. *@tormail.net: http://jhiwjjlqpyawmpjx.onion/
- Hax - Hacking, etc.
- Hashparty - Cracking site: http://3terbsb5mmmdyhse.onion/:HackBB - Forums for hacking, hosts some content: http://clsvtzwzdgzkjda7.onion/
- OnionWarez - Warez forum, kind of dead: http://dts563ge5y7c2ika.onion/
- Weird and Wonderful Old Stuff - Collection of old DOS and wIN software :D: http://xqz3u5drneuzhaeo.onion/users/dosbox2/
I2P
Main Article: I2P
The name I2P is derived from Invisible Internet Project, which, in pseudo-mathematical notation, is represented as I²P. It is described on their project page that I2P is an anonymous overlay network - a network within a network. It is intended to protect communication from dragnet surveillance and monitoring by third parties such as ISPs. I2P is used by many people who care about their privacy: activists, oppressed people, journalists and whistleblowers, as well as the average person. No network can be perfectly anonymous. The continued goal of I2P is to make attacks more and more difficult to mount. Its anonymity will get stronger as the size of the network increases and with ongoing academic review.
- I2P eepsites
- I2P2 - Main Project Site: http://i2p2.i2p
- Forum - Main Project Forum: http://forum.i2p/
- zzz - Main Developers' Site: http://zzz.i2p/
- killyourtv - Another developer site: http://killyourtv.i2p
- Planet - RSS Aggregator: http://planet.i2p/
- Salt - Crypto-munitions and tutorials http://salt.i2p/
- I2P-Bote - Serverless, encrypted e-mail plugin for I2P: http://i2pbote.i2p/
- PaTracker - Main torrent tracker: http://tracker2.postman.i2p/
- DifTracker - (French) torrent tracker: http://diftracker.i2p/
- id3nt - Microblogging: http://id3nt.i2p/
- Jisko - More microblogging: http://jisko.i2p/
- eepSites - Search Engine: http://eepsites.i2p/
Cellular surveillance
For your smartphone. Remember, regardless of what you do to your phone, there are some tradeoffs to your privacy and anonymity inherent in operating a device on a network you do not control.
Custom ROMs
- ParanoidAndroid
- Here is a helpful infographic.
CyanogenModLineage OS- There is a fork which comes with microG and F-Droid already installed, made by the same people who make microG.
- Here is a helpful infographic.
- GrapheneOS Only for Google Pixel devices.
Note: don't use gapps.
App stores
Search engines
Note: decentralized alternatives to search engines like YaCy are shit at the moment.
- Startpage (now merged with its other service, ixquick)
- DuckDuckGo
- Qwant
Maps
XPosed modules
Use the XPosed Framework with the XPrivacy Module.
- XPrivacy Module
- XPrivacyLua Module App made by the same developer as XPrivacy aimed at Android 6.0 or higher.
Firewalls
- AFWall+ (Android FireWall Plus) is a free firewall available for Android, which claims to restrict which apps may access the Internet over WiFi, data, and when roaming. Also useful for those without unlimited data plans: you can disallow data-intensive apps from using cellular data.
Miscellaneous
- Spoof your MAC address constantly.
- Create or obtain a faraday cage in the form of a phone case in order to block WiFi signals entirely. Example: https://offpocket.com/
Due to the distinct lack of physical WiFi togglers in mobile hardware, these are currently our only options from being tracked by corporations when out in meatspace.